Hackers delivered malware to Home windows and Mac customers by compromising their Web service supplier after which tampering with software program updates delivered over unsecure connections, researchers stated.
The assault, researchers from safety agency Volexity stated, labored by hacking routers or comparable sorts of machine infrastructure of an unnamed ISP. The attackers then used their management of the units to poison area title system responses for respectable hostnames offering updates for not less than six completely different apps written for Home windows or macOS. The apps affected had been the 5KPlayer, Fast Heal, Rainmeter, Partition Wizard, and people from Corel and Sogou.
These aren’t the replace servers you’re searching for
As a result of the replace mechanisms didn’t use TLS or cryptographic signatures to authenticate the connections or downloaded software program, the menace actors had been ready to make use of their management of the ISP infrastructure to efficiently carry out machine-in-the-middle (MitM) assaults that directed focused customers to hostile servers somewhat than those operated by the affected software program makers. These redirections labored even when customers employed non-encrypted public DNS providers reminiscent of Google’s 8.8.8.8 or Cloudflare’s 1.1.1.1 somewhat than the authoritative DNS server supplied by the ISP.
“That’s the enjoyable/scary half—this was not the hack of the ISPs DNS servers,” Volexity CEO Steven Adair wrote in an internet interview. “This was a compromise of community infrastructure for Web site visitors. The DNS queries, for instance, would go to Google’s DNS servers destined for 8.8.8.8. The site visitors was being intercepted to answer the DNS queries with the IP tackle of the attacker’s servers.”
In different phrases, the DNS responses returned by any DNS server can be modified as soon as it reached the infrastructure of the hacked ISP. The one means an finish person might have thwarted the assault was to make use of DNS over HTTPS or DNS over TLS to make sure lookup outcomes haven’t been tampered with or to keep away from all use of apps that ship unsigned updates over unencrypted connections.
Volexity supplied the next diagram illustrating the circulate of the assault:
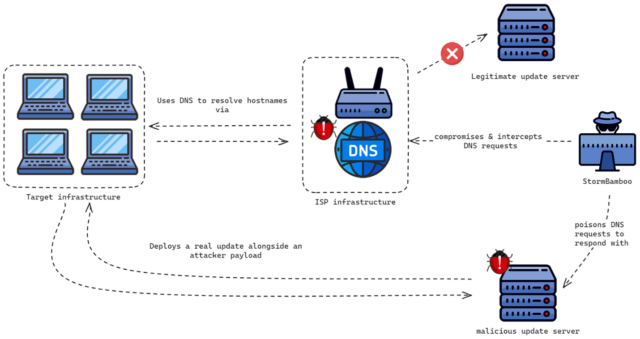
Volexity
For example, the 5KPlayer app makes use of an unsecure HTTP connection somewhat than an encrypted HTTPS one to verify if an replace is accessible and, if that’s the case, to obtain a configuration file named Youtube.config. StormBamboo, the title used within the business to trace the hacking group accountable, used DNS poisoning to ship a malicious model of the Youtube.config file from a malicious server. This file, in flip, downloaded a next-stage payload that was disguised as a PNG picture. In truth, it was an executable file that put in malware tracked underneath the names MACMA for macOS units or POCOSTICK for Home windows units.
MACMA first got here to gentle in 2021 post printed by Google’s Menace Evaluation Group, a group that tracks malware and cyberattacks backed by nation-states. The backdoor was written for macOS and iOS units and supplied a full suite of capabilities together with machine fingerprinting, display screen seize, file downloading and importing, execution of terminal instructions, audio recording, and keylogging.
POCOSTICK, in the meantime, has been in use since at least 2014. Final 12 months, safety agency ESET said the malware, which it tracked underneath the title MGBot, was used completely by a Chinese language-speaking menace group tracked as Evasive Panda.
ESET researchers decided that the malware was put in by respectable updates of benign software program, however they weren’t positive how that occurred. One risk, the researchers stated on the time, was by a supply-chain assault that changed the respectable updates with malicious ones on the very supply. The opposite potential state of affairs was by a MitM assault on the servers delivering the updates. Volexity’s findings now affirm that the latter rationalization is the proper one.
In not less than one case in the newest assaults, StormBamboo pressured a macOS machine to put in a browser plugin Volexity tracks underneath the title RELOADEXT. The extension masquerades as one which masses webpages to be suitable with Web Explorer. In truth, Volexity stated, it copies browser cookies and sends them to a Google Drive account managed by the attackers. The info was base64 encoded and encrypted utilizing the Superior Encryption Customary. Regardless of the care taken by the hackers, they nonetheless uncovered the client_id, client_secret, and refresh_token within the malicious extension.
One different approach Volexity noticed was StormBamboo’s use of DNS poisoning to hijack www.msftconnecttest.com , a site Microsoft makes use of to find out if Home windows units are actively linked to the Web. By changing the respectable DNS decision with an IP tackle pointing to a malicious website operated by the menace actors, they might intercept HTTP requests destined for any host.
Adair declined to determine the hacked ISP apart from to say it’s “not a giant big one or one you’d seemingly know.”
“In our case the incident is contained however we see different servers which are actively serving malicious updates however we have no idea the place they’re being served from,” he stated. “We suspect there are different lively assaults world wide we would not have purview into. This may very well be from an ISP compromise or a localized compromise to a company reminiscent of on their firewall.”
As famous earlier, there are a lot of choices for stopping these types of assaults past (1) eschewing all software program that updates unsecurely or (2) utilizing DNS over HTTPS or DNS over TPS. The primary methodology is probably going one of the best, though it seemingly means having to cease utilizing a most popular app in not less than some circumstances. The choice DNS configurations are viable, however for the time being are provided by solely a handful of DNS suppliers, with 8.8.8.8 and 1.1.1.1 being one of the best identified.
